Runtime Security
for AI Agents
Identity, enforcement, and credential protection for AI agents. No SDKs, no code changes, no way to bypass.
Your AI Agents Have a Security Blind Spot
Agents make autonomous decisions, call external APIs, and handle sensitive data. Today's security tools weren't built for agentic workloads.
of MCP implementations have injection flaws
Invariant Labs, 2025
of organizations lack visibility into AI data flows
Cisco AI Security Report, 2025
of AI agents deploy without formal approval
Splunk State of Security, 2025
Agents make network calls you can't see
Tool calls, API requests, and MCP connections are invisible to your security stack. Riptides logs every connection with identity, destination, and policy decision — automatically.
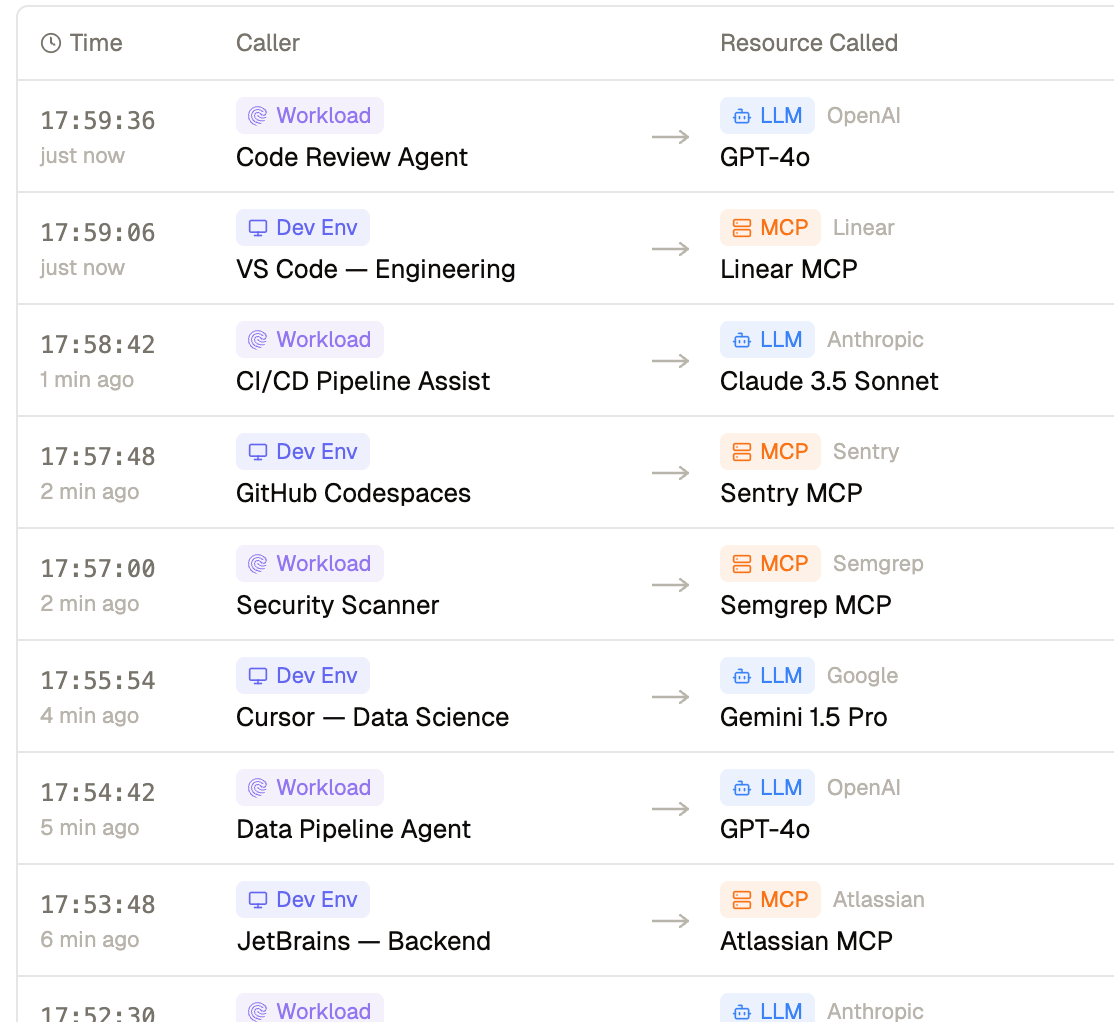
Capture identity-aware telemetry for every agent connection.
Surface real-time dashboards and anomaly alerts.
Generate compliance-ready audit trails tied to SPIFFE identity.
Stream to your existing stack — OpenTelemetry, Datadog, Elastic.
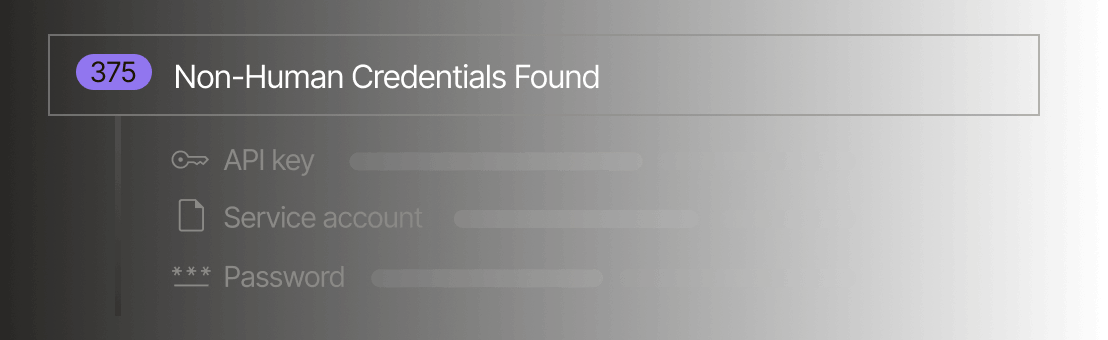
Agents hold credentials they shouldn't have
API keys get baked into configs, leaked in logs, and exfiltrated via prompt injection. Riptides injects credentials at the kernel level — agents never see, store, or handle secrets.
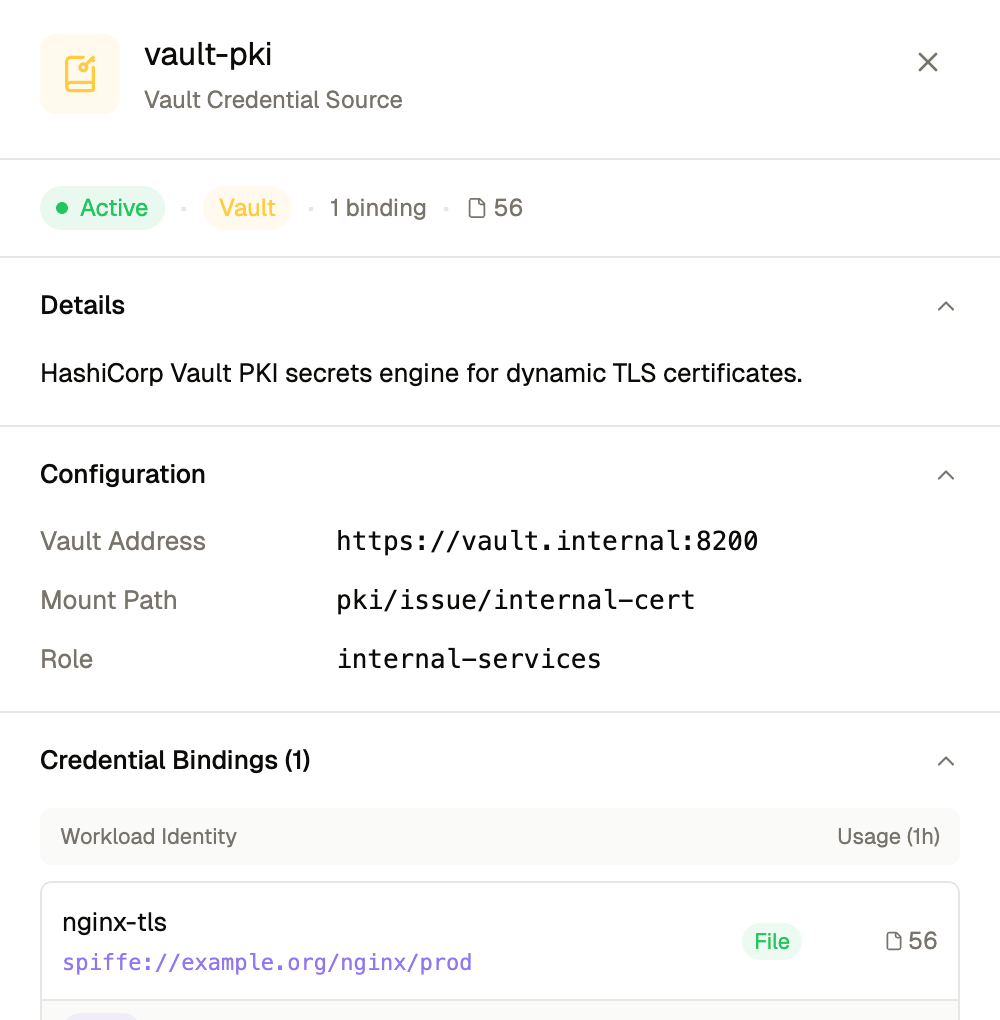
Keep secrets out of agent process memory entirely.
Eliminate keys from configs, logs, and environment variables.
Rotate credentials automatically without agent restarts.
Remove the risk of credential exfiltration via prompt injection.
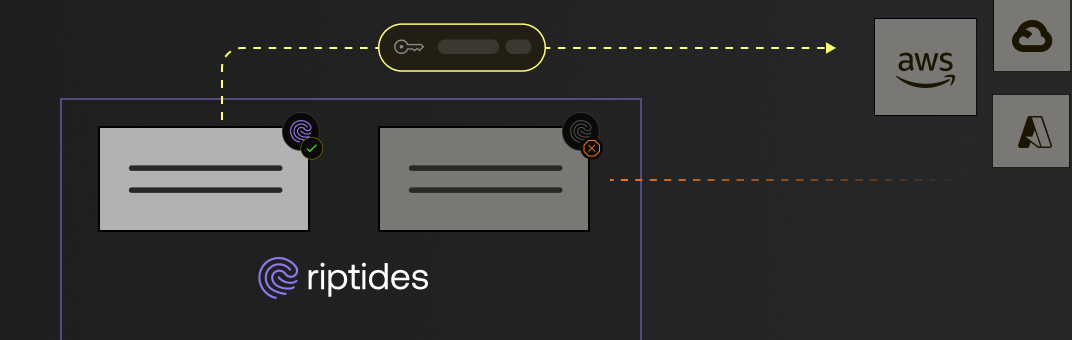
Agents connect to destinations you can't control
Without egress policy, any compromised agent can reach any endpoint. Riptides enforces per-agent access control at the kernel — agents cannot bypass it.
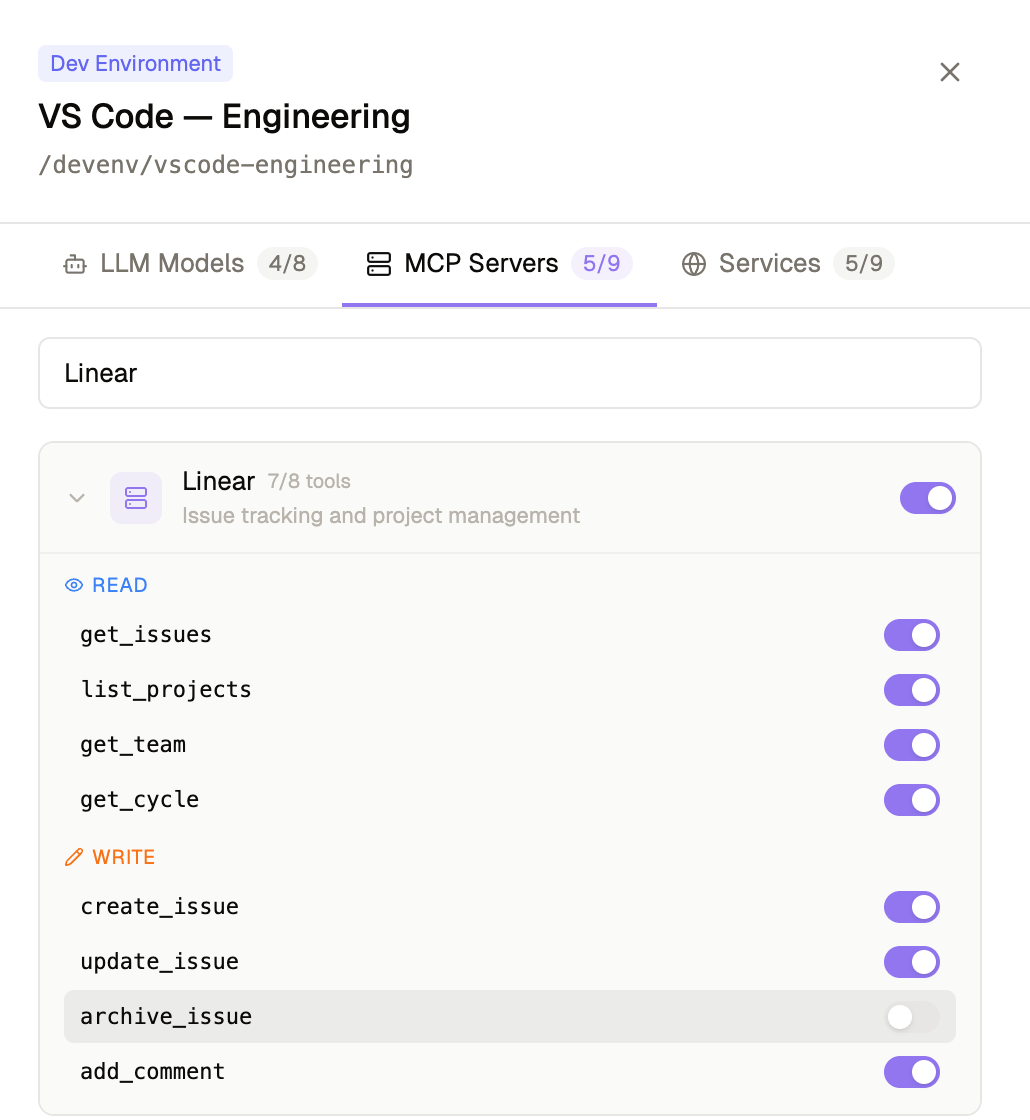
Define per-agent egress policies bound to agent identity.
Control MCP server connections per agent.
Restrict LLM API access by agent identity.
Block unauthorized destinations — default deny at the kernel.
How It Works:
Identity & Kernel Enforcement
Riptides deploys as a kernel module. No SDKs, no proxies, no code changes. It works with any agent framework, any language, any runtime.
Composite Identity
Every agent carries both a SPIFFE workload identity and the delegating human's context. Know which agent and on whose behalf.
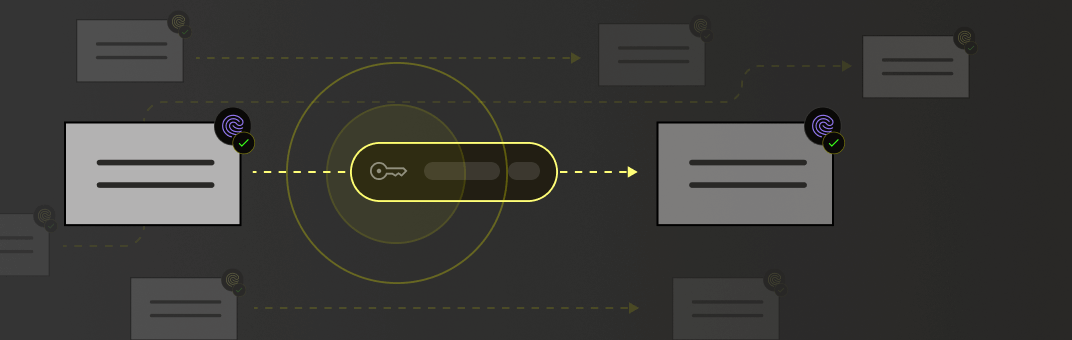
Kernel Module
Enforcement happens below the application layer. Agents cannot bypass, disable, or route around it.
Connection Telemetry
Every connection logged with agent identity, destination, policy decision, and credential used. Streams to your SIEM.
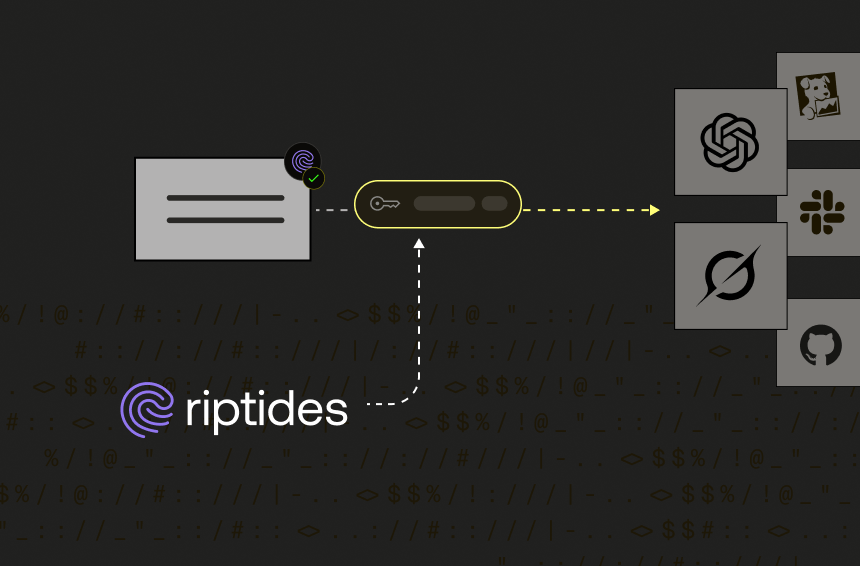
Credential Injection
Inject API keys, SigV4 signatures, and bearer tokens into requests in kernel space. Agents never touch secrets.
Egress Policy
Per-agent allow/deny rules for every destination. Default deny — only explicitly allowed connections proceed.
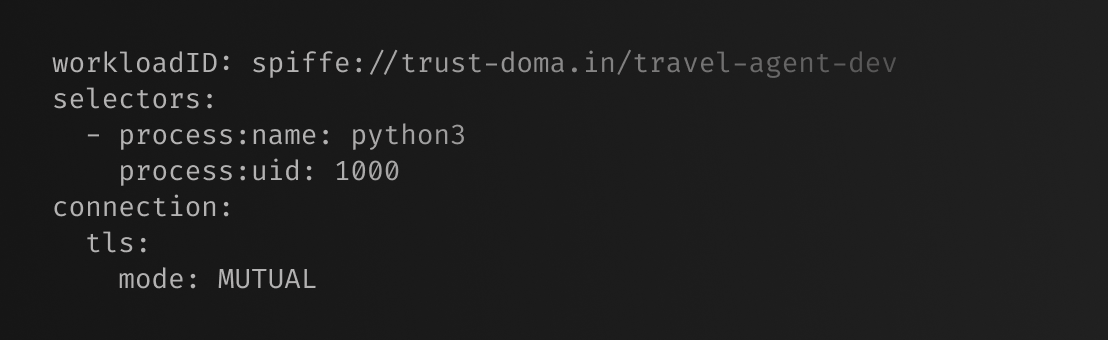
Automatic mTLS
Every agent-to-agent and agent-to-service connection encrypted and authenticated. No TLS config required.
Ready to secure your
workloads?
Kernel-level identity and enforcement. No code changes. Deploy in minutes.