Runtime Identity & Security for Every Workload.
From AI agents to infrastructure — identity, credential protection, and policy enforcement at the kernel. No SDKs, no code changes.
One Platform. Every Workload.
The same kernel-level identity and enforcement for AI agents and traditional infrastructure. SPIFFE identity, credential injection, mTLS, and policy — deployed once, securing everything.
Agentic AI Security
AI agents make autonomous decisions, call external APIs, and handle sensitive credentials. They need per-agent identity, egress control, and credential protection that can't be bypassed.
Workload IAM
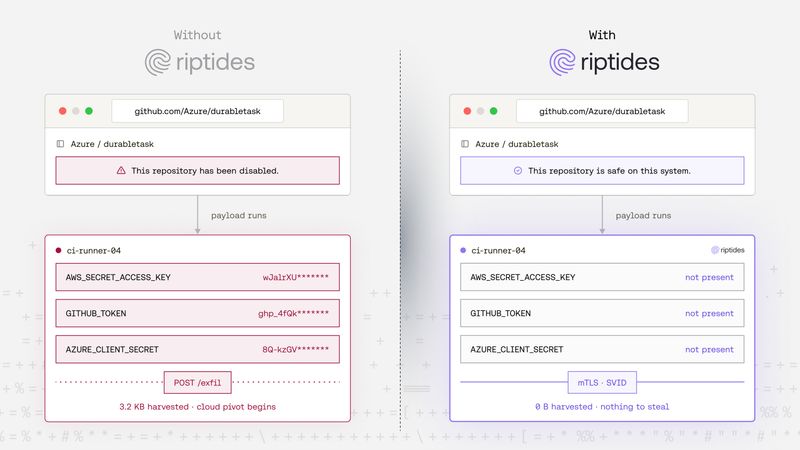
Machine credentials are the #1 breach vector. Replace static secrets with SPIFFE identity, automatic mTLS, and cloud federation — enforced at the kernel.
Built on One Foundation
Both products share the same kernel-level enforcement engine. Deploy once, secure every workload type.
SPIFFE Identity
Every workload — agent or service — gets a SPIFFE identity. Short-lived, auto-rotated, kernel-attested.
Kernel Enforcement
Security policies enforced below the application layer. No SDK, no sidecar, no proxy. Workloads cannot bypass it.
Zero-Touch Deployment
No code changes, no framework integrations. Works with any language, any runtime, any orchestrator.
Unified Telemetry
Every connection logged with identity, destination, and policy decision. Streams to your existing observability stack.
Ready to secure your
workloads?
Kernel-level identity and enforcement. No code changes. Deploy in minutes.
Integrations
Connect with your existing infrastructure and tools.
Kubernetes
Build identities by relying on Kubernetes metadata.
SPIFFE
Integrate with existing systems using SPIFFE and standard SVIDs.
OpenAI
Securely inject API keys into OpenAI agents at runtime.
Grok
Provide Grok agents with API keys without exposing secrets.
AWS
Federate trust across AWS with IAM Roles Anywhere.
Google Cloud
Give workloads access to Google Cloud using Workload Identity Federation
Latest Riptides News
Deep dives on secure identity, AI agent infrastructure, and what's next for workload-to-workload trust.
Frequently Asked Questions
Who is Riptides for?
Riptides is built for security, platform, and infrastructure teams securing both AI agents and traditional workloads. Whether your agents make API calls and connect to MCP servers, or your services need secretless credentials and mTLS — Riptides secures those connections at the kernel level with no code changes.
What's the difference between Agentic AI Security and Workload IAM?
Both products share the same kernel-level enforcement engine. Agentic AI Security focuses on per-agent identity, egress control for tool calls, and credential protection for AI agents. Workload IAM focuses on secretless infrastructure, automatic mTLS, and identity federation for traditional services and CI/CD pipelines. Many teams use both.
Which agent frameworks and languages does Riptides work with?
All of them. Riptides operates at the kernel level, below the application layer, so it works with LangChain, CrewAI, AutoGen, OpenAI Agents SDK, MCP-based agents, and any custom agent or service that makes network calls. Any language, any framework — no integration required.
How is Riptides different from a service mesh or AI gateway?
Service meshes and AI gateways operate at the application or network layer — they require sidecars, proxy configuration, or routing changes. Riptides enforces security at the kernel. No sidecars, no proxies, no code changes. Workloads cannot bypass, disable, or route around it.
What makes kernel-level enforcement better?
Kernel-level enforcement means identities are tied directly to running processes, not to network locations or application logic. It's fully independent of both the application code and the underlying network stack. This prevents identity spoofing and blocks unauthorized connections even from compromised processes.
How does secretless credential injection work?
When a workload makes an outbound request, the Riptides kernel module intercepts it, matches the workload's SPIFFE identity to a credential binding, fetches the credential from your secret store (Vault, K8s Secrets, AWS Secrets Manager), and injects it into the request. The credential never enters process memory — it exists only in kernel space for the duration of the request.
Is Riptides compatible with my existing infrastructure?
Yes. Riptides integrates with Kubernetes and container platforms, supports open standards like SPIFFE and mTLS, federates to AWS/GCP/Azure via OIDC, and streams telemetry to your existing observability stack (OpenTelemetry, Datadog, Splunk, Elastic). It can be introduced gradually without requiring a full platform overhaul.
Does Riptides store secrets outside my environment?
No. The Riptides control plane never stores your secrets or credentials. Identity issuance, credential injection, and policy enforcement all happen within your environment. Sensitive data never leaves your trust boundary.
Will Riptides be open source?
Yes. We plan to open source the core of Riptides, including the kernel module that powers identity enforcement. Open sourcing increases transparency and makes it easier for teams to audit and adopt the technology with confidence.