The 200-Day TLS Era Has Begun — Is Your Infrastructure Ready?
As of March 15, 2026, the maximum validity period for publicly trusted TLS/SSL certificates officially dropped from 398 days to 200 days. If you haven’t felt the impact yet, you will soon — the next renewal cycle is coming faster than you think.
This isn’t a decision by any single certificate authority. It’s an industry-wide mandate from the CA/Browser Forum (CABF), the governing body made up of certificate authorities, browser vendors, and OS providers. The goal is clear: make the internet more secure by forcing faster rotation, better validation hygiene, and — critically — automation.
Further reading:
- DigiCert — TLS Certificate Lifetimes Will Officially Reduce to 47 Days
- Sectigo — The 200-Day SSL/TLS Certificate Change
- SSL.com — The 200-Day Certificate Deadline
What Actually Changed
Any certificate issued on or after March 15, 2026 must comply with the new 200-day maximum. It’s the issue date, not the renewal request date, that determines compliance. If you ordered a renewal before the deadline but it wasn’t issued in time, it’s still subject to the new limit.
This affects more than just public websites. APIs, load balancers, application services, edge environments — anything using publicly trusted TLS is now on a faster clock.
In practical terms: you’re renewing certificates more than twice as often as before. What was already a demanding process has become genuinely unmanageable without the right automation in place.
This Is Just the Beginning
The 200-day limit isn’t the destination — it’s the first step on a much shorter road:
- March 15, 2027 — maximum validity drops to 100 days
- March 15, 2029 — maximum validity drops to 47 days
At 47 days, manual certificate management doesn’t just become difficult — it becomes effectively impossible at any meaningful scale. The industry is sending a clear message: automation is no longer optional, it’s the baseline.
Why Shorter Certificates Are Actually Good
The security rationale is straightforward. Long-lived certificates are a silent risk. A compromised or misissued certificate valid for 398 days gives attackers nearly 13 months of potential exposure. Shortening that window reduces the blast radius significantly.
The real-world consequences of long-lived certificates are well documented. In 2023, the Chinese APT group Bronze Starlight was caught signing malware with a stolen code-signing certificate belonging to Ivacy VPN — a certificate that remained valid and trusted for months before DigiCert eventually revoked it. The attackers used it to bypass security tools and blend in with legitimate software traffic, completely undetected. A short-lived, automatically rotated certificate would have rendered the stolen key useless far sooner.
There’s also a cryptographic agility argument. As post-quantum cryptography standards continue to mature, the ability to rotate certificates quickly — without waiting for year-long validity windows to expire — becomes increasingly critical. Shorter lifetimes mean the ecosystem can adapt faster when trust requirements or algorithms change.
More frequent renewals also mean more frequent domain and organization validation, keeping certificate holders accountable and ensuring that who controls a domain today is still who controls it tomorrow.
The Operational Problem No One Talks About Enough
Here’s what 200-day certificate management actually looks like without automation: a constant cycle of CSR generation, domain validation, installation, and testing — running in parallel across every endpoint in your infrastructure. APIs, internal services, load balancers, Kubernetes ingress controllers, legacy apps. Each one with its own expiry date, each one a potential outage if someone misses it.
At 200 days you might still get away with careful spreadsheet tracking and calendar reminders. At 100 days that gets painful. At 47 days it breaks entirely. The teams that are struggling today are the ones who will be in crisis in 2027.
The real problem isn’t the renewal itself — it’s the lack of visibility. Most organizations don’t have a clear inventory of every certificate they own, where it’s deployed, and when it expires. Without that foundation, automation has nothing to build on.
The Better Model: Identity-Native TLS with SPIFFE and SVIDs
One of the most important shifts happening alongside the cert lifecycle changes is a move away from managing certificates as static artifacts and toward treating them as expressions of workload identity. This is the architectural direction the industry is heading — and it’s the model Riptides is built around.
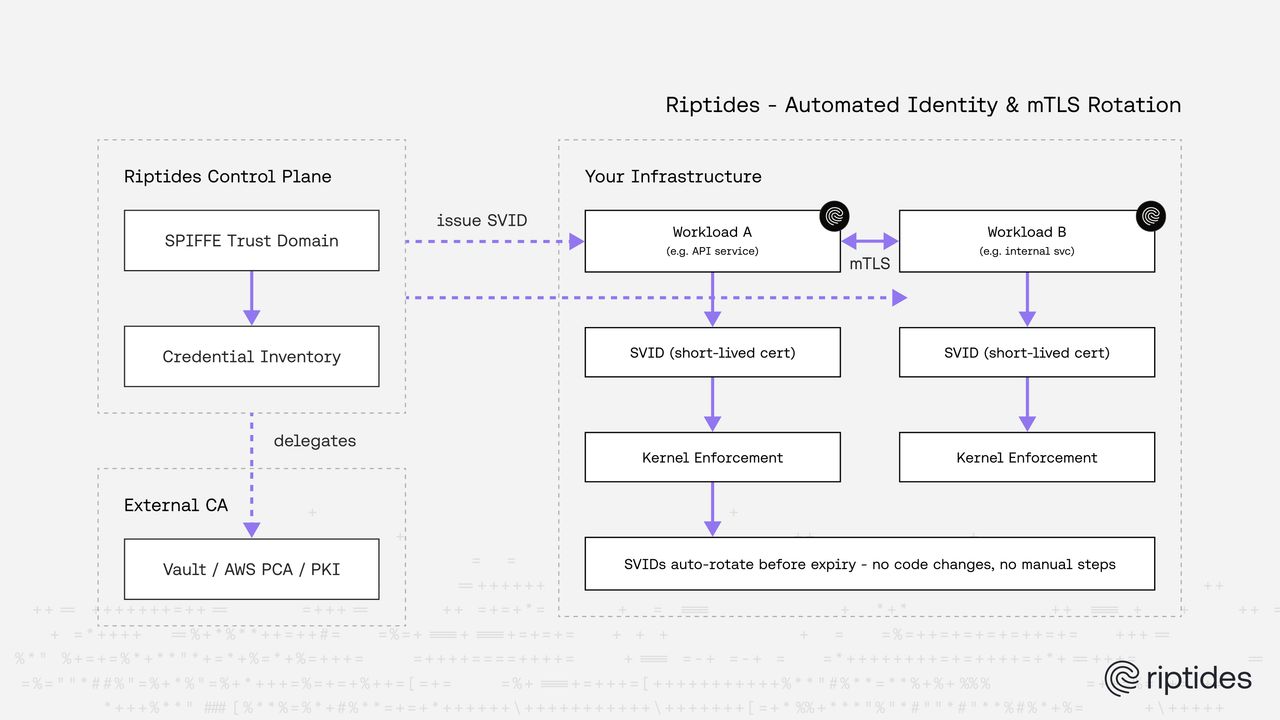
The SPIFFE standard (Secure Production Identity Framework for Everyone) addresses exactly this. Instead of issuing long-lived TLS certificates tied to a hostname or IP, SPIFFE assigns every workload a cryptographically verifiable identity — called an SVID (SPIFFE Verifiable Identity Document). SVIDs are short-lived by design, automatically rotated, and scoped to the workload rather than the network location.
This is a fundamentally better model for the world we’re moving into. Rather than asking “is this certificate still valid?”, you’re asking “is this the workload it claims to be?” Trust is tied to identity, not to infrastructure topology. Because SVIDs are short-lived and automatically rotated, the operational burden of the 200-day — and eventually 47-day — world largely disappears. The platform handles rotation continuously, invisibly, and correctly.
Riptides implements this model natively. Every workload and AI agent in your infrastructure gets a SPIFFE identity, and every connection is mutually authenticated using that identity. The CA that signs those identities can live inside the Riptides control plane or be delegated to an external system like HashiCorp Vault or AWS Private CA — whatever fits your existing PKI. Trust extends naturally across cloud providers, clusters, and environments through federated SPIFFE trust domains, with no manual certificate tracking required.
This Trend Isn’t Just About Public Certs
It’s worth being precise about scope: the CA/Browser Forum changes apply specifically to publicly trusted TLS certificates — the ones securing your public websites, external APIs, and customer-facing endpoints. For those, the tooling answer is a solid CLM platform with ACME automation.
But the same underlying philosophy — short-lived credentials, continuous rotation, identity over infrastructure — is spreading well beyond public certs. Internal service-to-service communication, workload-to-workload trust, AI agent authentication: these are all areas where the industry is moving toward the same model, driven by security rather than regulatory mandate.
This is the space Riptides is built for. It’s not a replacement for your CA or cert manager — it’s an identity fabric for the east-west traffic that traditional cert management doesn’t reach. Riptides assigns every workload and AI agent a short-lived SPIFFE identity, automates mTLS between services at the kernel level without touching application code, and maintains a real-time inventory of all non-human credentials across your environment.
The CA/Browser Forum is forcing short-lived cert rotation onto public infrastructure. Riptides applies that same model to internal workloads — where the tooling has historically lagged furthest behind. If you’re rethinking your cert strategy for 2027 and beyond, it’s worth thinking about both halves of the problem. See how Riptides handles the internal side.
What To Do Right Now
Even if your current certificates are still valid under the old 398-day limit, the clock is ticking. Here’s where to start:
1. Audit your certificate estate. Identify every public TLS certificate across your infrastructure — load balancers, APIs, ingress controllers, internal services. Record expiry dates, validation types, and who owns each renewal.
2. Find your manual gaps. Which certificates are renewed by email, spreadsheet, or ticket? Those are your highest-risk assets under the new regime.
3. Move toward automation. ACME-based workflows and certificate lifecycle management (CLM) platforms are the minimum. Identity-native platforms that eliminate long-lived certs entirely are the longer-term answer.
4. Plan for 2027, not just today. The 200-day limit is manageable. The 100-day limit arriving in March 2027 is where manual processes start to break. Build for that, not for the deadline you just passed.
The 398-day certificate era is over. The infrastructure that thrives in what comes next is the infrastructure that was already treating rotation as a continuous, automated process — not a calendar event.
If you enjoyed this post, follow us on LinkedIn and X for more updates. If you'd like to see Riptides in action, get in touch with us for a demo.
Ready to secure your
workloads?
Kernel-level identity and enforcement. No code changes. Deploy in minutes.